MY TAKE: Why monetizing data lakes will require applying ‘attribute-based’ access rules to encryption
The Last Watchdog
JUNE 2, 2021
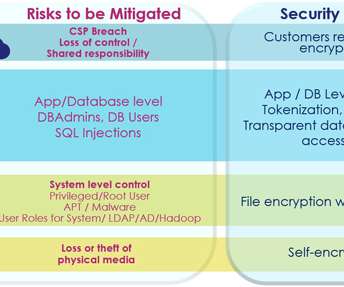
Each private key serves a narrow function: it gives the same type of authenticity and level of access to each user. All the attacker needs to do, he says, is to take over the account of a legitimate user to attain deep access to a lot of sensitive information stored in the cloud. Attribute-based access. This creates exposure.















Let's personalize your content