How to Meet Phishing-Resistant MFA
Thales Cloud Protection & Licensing
JULY 31, 2023
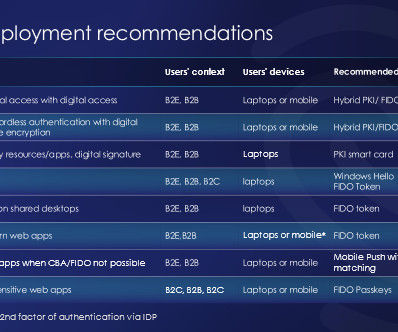
How to Meet Phishing-Resistant MFA madhav Tue, 08/01/2023 - 05:18 Incorporating multi-factor authentication (MFA) as a fundamental security measure for your organization is now considered standard practice. How can we combine the best of two worlds in a single phishing-resistant MFA solution? It's a sensible decision to utilize MFA.




















Let's personalize your content