Mozi infections will slightly decrease but it will stay alive for some time to come
Security Affairs
SEPTEMBER 1, 2021
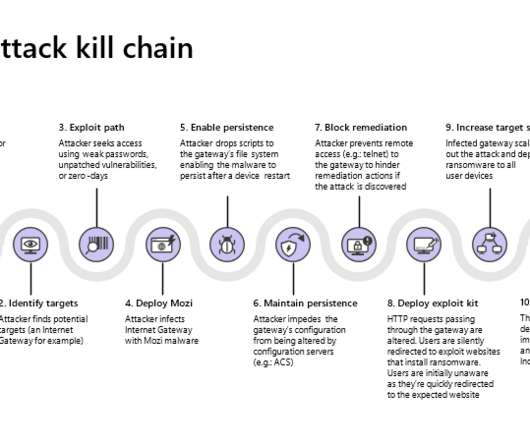
Earlier in August, Microsoft researchers reported that the Mozi botnet was improved by implementing news capabilities to target network gateways manufactured by Netgear, Huawei, and ZTE. In the diagram below we show just one example of how the vulnerabilities and newly discovered persistence techniques could be used together.














Let's personalize your content