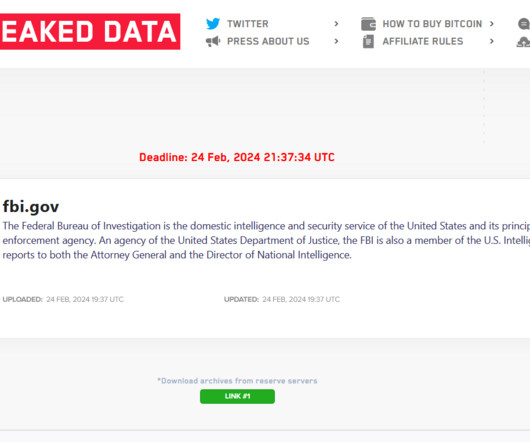
U.S. Charges 4 Chinese Military Officers in 2017 Equifax Hack
Krebs on Security
FEBRUARY 10, 2020
as members of the PLA’s 54 th Research Institute, a component of the Chinese military. Attorney General Bill Barr said at a press conference today that the Justice Department doesn’t normally charge members of another country’s military with crimes (this is only the second time the agency has indicted Chinese military hackers).


























Let's personalize your content