How Shady Chinese Encryption Chips Got Into the Navy, NATO, and NASA
WIRED Threat Level
JUNE 15, 2023
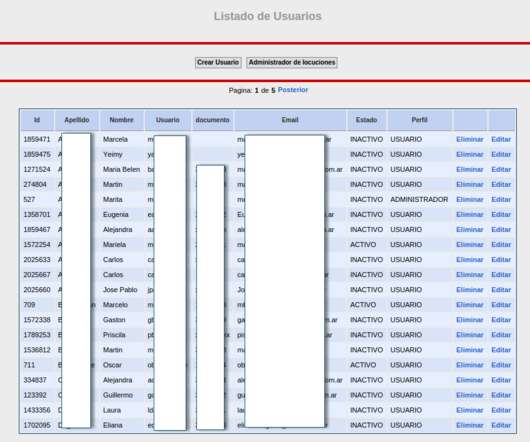
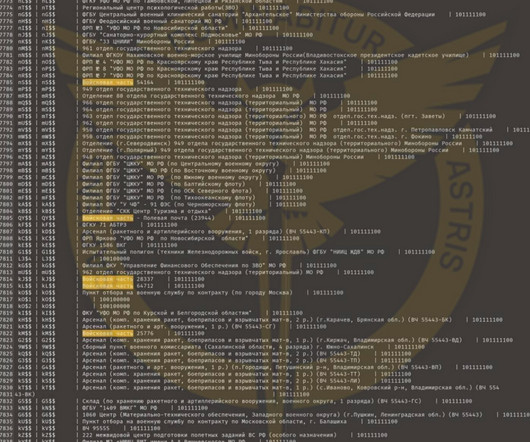
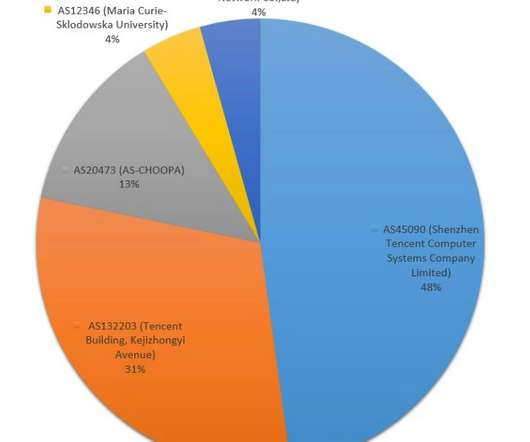
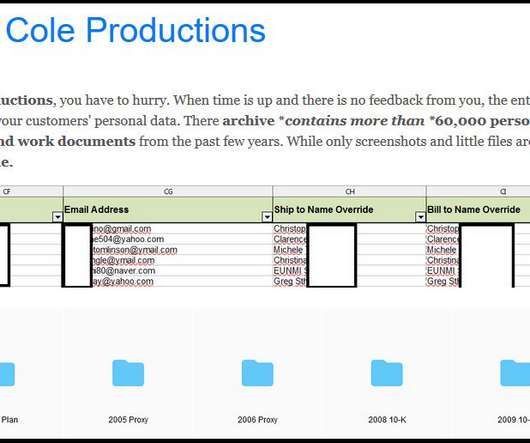
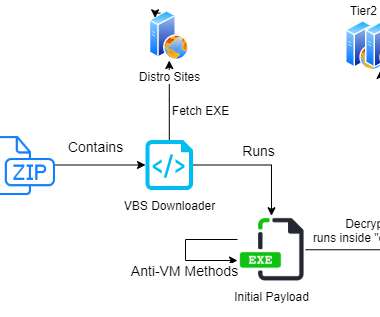
The US government warns encryption chipmaker Hualan has suspicious ties to China’s military. Yet US agencies still use one of its subsidiary’s chips, raising fears of a backdoor.






























Let's personalize your content