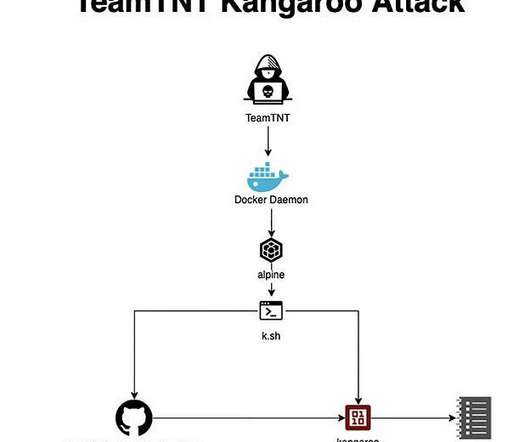
Threat Group TeamTNT Returns with New Cloud Attacks
eSecurity Planet
SEPTEMBER 21, 2022
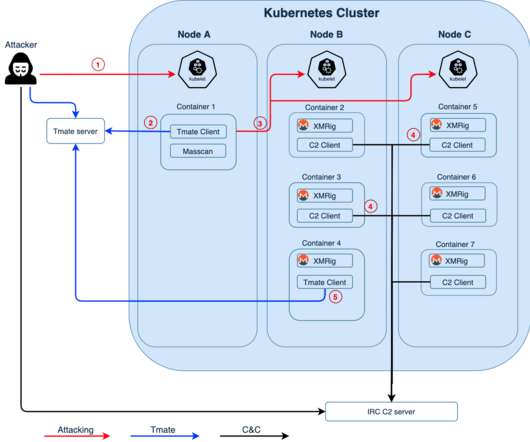
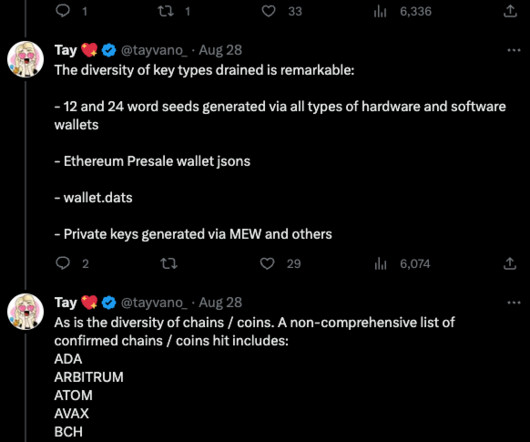
A retired threat actor has returned with new attacks aimed at the cloud, containers – and encryption keys. All internet communications, including SSL and SSH, rely on private and public keys for encryption. It’s the fundamental principle of modern cryptography: encryption must be a one-way operation. format(len(targets)).























Let's personalize your content