2021 Security Budgets: Top Priorities, New Realities
Dark Reading
DECEMBER 14, 2020
An unprecedented 2020 has shaken up security leaders' usual list of must-have technologies. What's on the horizon? They share with us their spending plans for 2021.

Dark Reading
DECEMBER 14, 2020
An unprecedented 2020 has shaken up security leaders' usual list of must-have technologies. What's on the horizon? They share with us their spending plans for 2021.

Data Breach Today
DECEMBER 13, 2020
SolarWinds: Flawed Updates in Orion Platform May be Source of Attacks The U.S. Commerce Department confirmed on Sunday it had been targeted by hackers, and the U.S. Treasury has also reportedly been struck. The intrusions may be linked to a vulnerability in updates SolarWinds made to its Orion network monitoring product earlier this year, which could mean a broad impact.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
WIRED Threat Level
DECEMBER 16, 2020
Despite years of warning, the US still has no good answer for the sort of “supply chain” attack that let Russia run wild.
Krebs on Security
DECEMBER 18, 2020
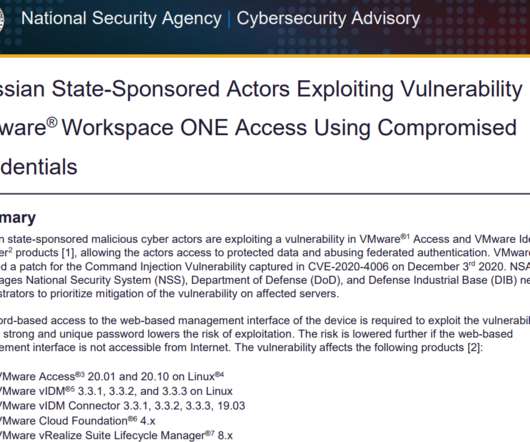
U.S. government cybersecurity agencies warned this week that the attackers behind the widespread hacking spree stemming from the compromise at network software firm SolarWinds used weaknesses in other, non-SolarWinds products to attack high-value targets. According to sources, among those was a flaw in software virtualization platform VMware , which the U.S.

Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.

The Last Watchdog
DECEMBER 13, 2020
One legacy of the ongoing global pandemic is that companies now realize that a secured and well-supported remote workforce is possible. Recently, the University of Illinois and the Harvard Business School conducted a study, and 16% of companies reported switching their employees to work at home from offices at least twice a week. Related: SASE translates into secure connectivity.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

AIIM
DECEMBER 17, 2020
Why Business Automation Matters. Business process management is an essential part of a growing business. Without it, organizations could face low customer satisfaction, lack of communication, and a higher chance of error. By letting computers take care of menial, repetitive day-to-day tasks, automation can save businesses money and time. Without the human component in handling data, there is a lower chance of error.

Krebs on Security
DECEMBER 16, 2020
A key malicious domain name used to control potentially thousands of computer systems compromised via the months-long breach at network monitoring software vendor SolarWinds was commandeered by security experts and used as a “killswitch” designed to turn the sprawling cybercrime operation against itself, KrebsOnSecurity has learned. Austin, Texas-based SolarWinds disclosed this week that a compromise of its software update servers earlier this year may have resulted in malicious code
Security Affairs
DECEMBER 12, 2020
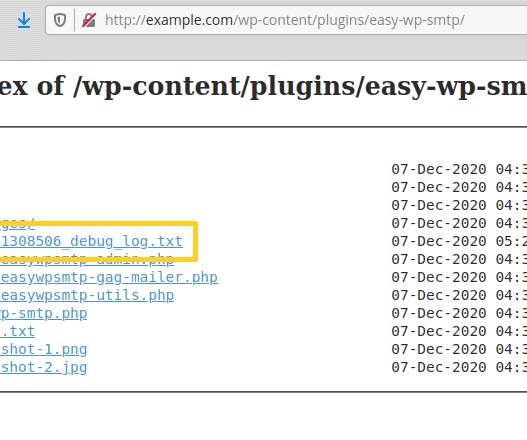
Threat actors are actively exploiting a zero-day vulnerability in the popular Easy WP SMTP WordPress plugin installed on more than 500,000 sites. Hackers are actively exploiting a zero-day vulnerability in the popular Easy WP SMTP WordPress plugin to reset passwords for admin accounts. The SMTP WordPress plugin is installed on more than 500,000 sites, but despite the security patch has been released earlier this week many sites are yet to be patched.

Data Breach Today
DECEMBER 14, 2020
Fellow Victim FireEye Traces Breaches to Trojanized SolarWinds Software Updates The U.S. Commerce Department confirmed on Sunday it had been targeted by hackers, and the U.S. Treasury has also reportedly been struck. The intrusions appear linked to subverted software updates for SolarWinds' Orion network monitoring product, which is widely used by companies and the U.S. government.

Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.

Schneier on Security
DECEMBER 18, 2020
The NSA has published an advisory outlining how “malicious cyber actors” are “are manipulating trust in federated authentication environments to access protected data in the cloud.” This is related to the SolarWinds hack I have previously written about , and represents one of the techniques the SVR is using once it has gained access to target networks.

Dark Reading
DECEMBER 17, 2020
Extended Detection and Response (XDR) could be the security management technology of your dreams.or not. What makes this technical 'evolution' so interesting to so many companies?
Security Affairs
DECEMBER 15, 2020
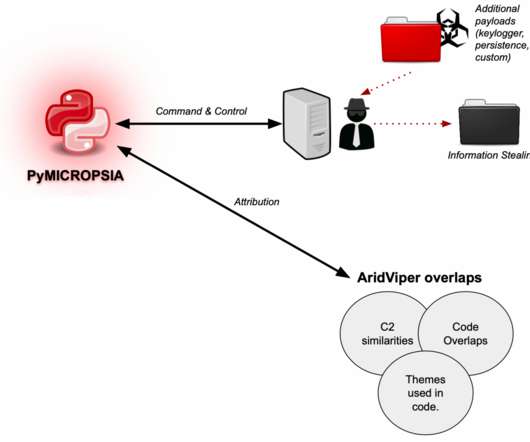
Experts discovered a new Windows info-stealer, named PyMICROPSIA, linked to AridViper group that is rapidly evolving to target other platforms. Experts from Palo Alto Networks’s Unit 42 discovered a new Windows info-stealing malware, named PyMICROPSIA, that might be used soon to also target Linux and macOS systems. Experts spotted the PyMICROPSIA info stealer while investigating attacks of the AridViper group (also tracked as Desert Falcon and APT-C-23 ).

Data Breach Today
DECEMBER 18, 2020
Cybercriminals Are Using Phone Calls to Pressure Victims The FBI is warning of increased activity - including disruption of a police dispatch system - by the operators of DoppelPaymer, a ransomware variant linked to high-profile attacks over the last several months. The cybercriminals also are calling victims to pressure them into paying ransoms.

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

Schneier on Security
DECEMBER 18, 2020
Gizmodo is reporting that schools in the US are buying equipment to unlock cell phones from companies like Cellebrite: Gizmodo has reviewed similar accounting documents from eight school districts, seven of which are in Texas, showing that administrators paid as much $11,582 for the controversial surveillance technology. Known as mobile device forensic tools (MDFTs), this type of tech is able to siphon text messages, photos, and application data from student’s devices.
Threatpost
DECEMBER 18, 2020
Examining the backdoor's DNS communications led researchers to find a government agency and a big U.S. telco that were flagged for further exploitation in the spy campaign.

Security Affairs
DECEMBER 18, 2020
Threat actors continue to trade critical medical data in the Dark Web while organizations are involved in the response to the COVID-19 pandemic. Cybercrime organizations continue to be very active while pharmaceutical organizations are involved in the development of a COVID-19 vaccine and medicines to cure the infections. Experts from Cyble discovered in several forums on the dark web, the offer for enormous repositories of critical medical that wee stolen from multiple organizations.

Data Breach Today
DECEMBER 16, 2020
Trace Fooshee of Aite Group Provides an Outlook of Key Trends What kind of financial fraud can we expect in the year ahead? Trace Fooshee of Aite Group offers a forecast based on a new report.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.

Schneier on Security
DECEMBER 17, 2020
The New York Times has more details. About 18,000 private and government users downloaded a Russian tainted software update – a Trojan horse of sorts – that gave its hackers a foothold into victims’ systems, according to SolarWinds, the company whose software was compromised. Among those who use SolarWinds software are the Centers for Disease Control and Prevention, the State Department, the Justice Department, parts of the Pentagon and a number of utility companies.
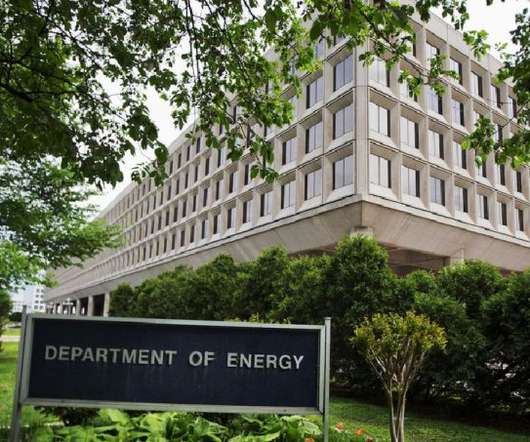
Threatpost
DECEMBER 17, 2020
Sources said the DoE suffered "damage" in the attack, which also likely extends beyond the initially known SolarWinds Orion attack vector.
Security Affairs
DECEMBER 15, 2020
Norwegian cruise company Hurtigruten disclosed a cyber attack that impacted its entire worldwide digital infrastructure. The Norwegian cruise company Hurtigruten announced its entire worldwide digital infrastructure was the victim of a cyber attack. “It’s a serious attack,” said the Hurtigruten’s chief digital officer Ole-Marius Moe-Helgesen in a statement. “The entire worldwide digital infrastructure of Hurtigruten seems to have been hit.” “The attack s

Data Breach Today
DECEMBER 18, 2020
The latest edition of the ISMG Security Report features an analysis of what we know so far about the impact of the SolarWinds supply chain hack and how to respond.

Advertisement
Are you trying to decide which entity resolution capabilities you need? It can be confusing to determine which features are most important for your project. And sometimes key features are overlooked. Get the Entity Resolution Evaluation Checklist to make sure you’ve thought of everything to make your project a success! The list was created by Senzing’s team of leading entity resolution experts, based on their real-world experience.

Schneier on Security
DECEMBER 15, 2020
This is interesting : Toward the end of the second incident that Volexity worked involving Dark Halo, the actor was observed accessing the e-mail account of a user via OWA. This was unexpected for a few reasons, not least of which was the targeted mailbox was protected by MFA. Logs from the Exchange server showed that the attacker provided username and password authentication like normal but were not challenged for a second factor through Duo.

IT Governance
DECEMBER 14, 2020
In a Christmas in which we’ll be relying on technology more than ever – whether for online shopping or staying in contact with loved ones – we must all be aware of cyber security threats. According to the UK government , the 2019 festive period saw online shoppers in England and Wales lose, on average, £775. That’s why it has created the Cyber Aware campaign , which contains guidance on topics such as password security and software updates that will protect you from criminals’ most common attack
Security Affairs
DECEMBER 16, 2020
Microsoft, FireEye, and GoDaddy have partnered to create a kill switch for the Sunburst backdoor that was employed in the recent SolarWinds hack. Microsoft, FireEye, and GoDaddy have created a kill switch for the Sunburst backdoor that was used in SolarWinds supply chain attack. Last week, Russia-linked hackers breached SolarWinds, the attackers had used a trojanized SolarWinds Orion business software updates to distribute the backdoor tracked as SUNBURST (aka Solarigate (Microsoft)).
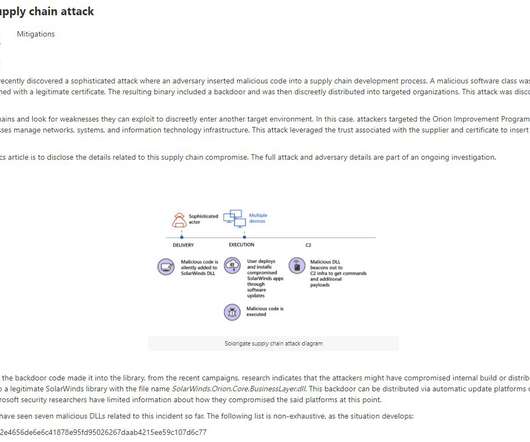
Data Breach Today
DECEMBER 14, 2020
Mitigation Advice Includes Immediate Updates and Scans for Signs of Compromise Warning: The breach of FireEye disclosed last week traces to a sophisticated campaign involving Trojanized versions of SolarWinds Orion software used by hundreds of large businesses and government agencies. Experts are urging users to immediately upgrade the software and begin looking for signs of compromise.

Advertisement
“Reimagined: Building Products with Generative AI” is an extensive guide for integrating generative AI into product strategy and careers featuring over 150 real-world examples, 30 case studies, and 20+ frameworks, and endorsed by over 20 leading AI and product executives, inventors, entrepreneurs, and researchers.

Schneier on Security
DECEMBER 17, 2020
Sophisticated spyware, sold by surveillance tech companies to Mexican government agencies, are ending up in the hands of drug cartels : As many as 25 private companies — including the Israeli company NSO Group and the Italian firm Hacking Team — have sold surveillance software to Mexican federal and state police forces, but there is little or no regulation of the sector — and no way to control where the spyware ends up, said the officials.
Dark Reading
DECEMBER 16, 2020
Redirecting a user to a trusted server buys a secure email gateway company some time while it decides whether a URL is malicious -- but there are avoidable drawbacks to this approach.

Security Affairs
DECEMBER 17, 2020
FBI says DoppelPaymer ransomware gang is harassing victims who refuse to pay, threatening to send individuals to their homes. FBI is warning of a new escalation in the extortion activities of the DoppelPaymer ransomware gang, the operators have been calling victims, threatening to send individuals to their homes if they don’t pay the ransom. According to a private industry notification alert (PIN), sent by the FBI to private organizations, the Bureau is aware of extortion activities that h
Let's personalize your content