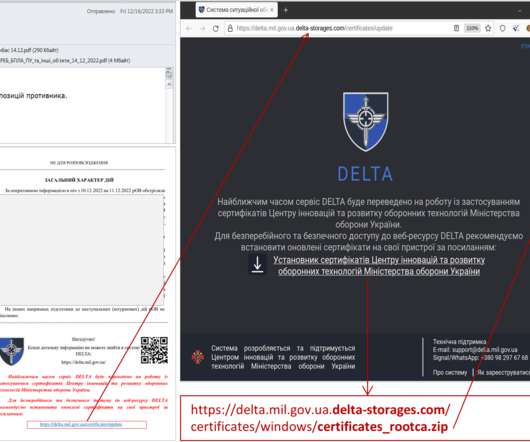
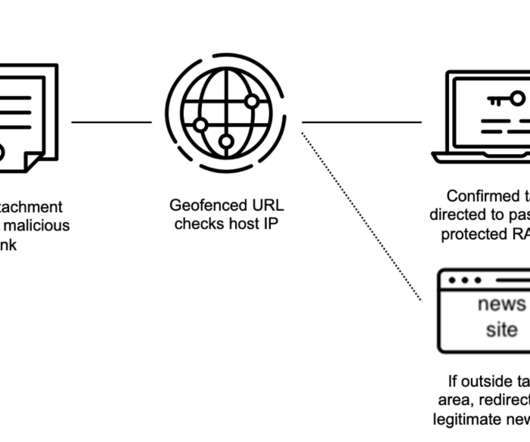
UAC-0142 APT targets Ukraine’s Delta military intelligence program
Security Affairs
DECEMBER 20, 2022
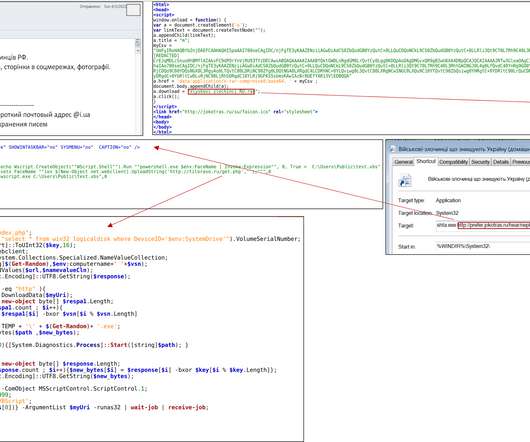
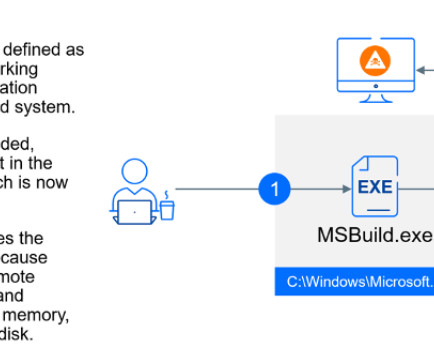
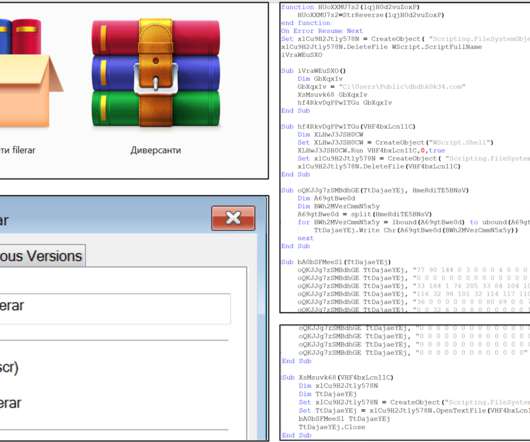
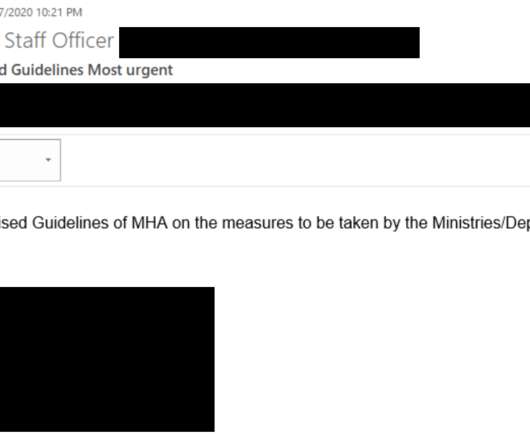
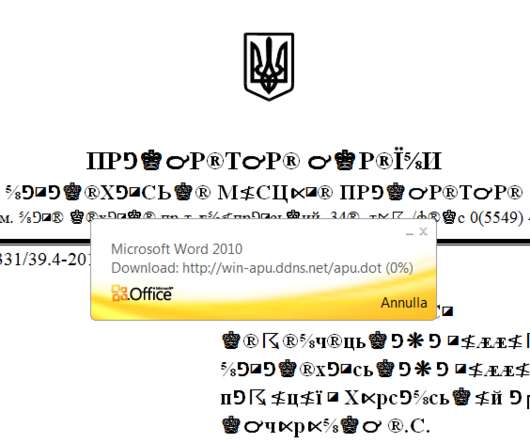
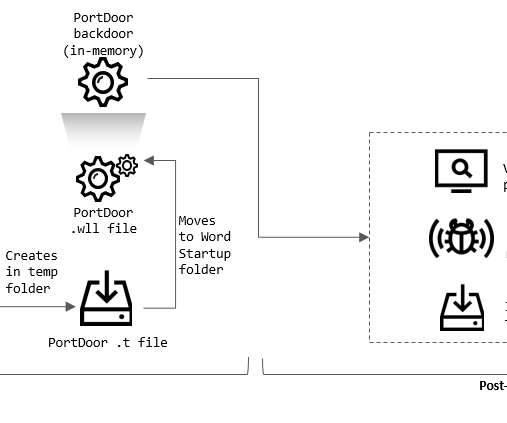
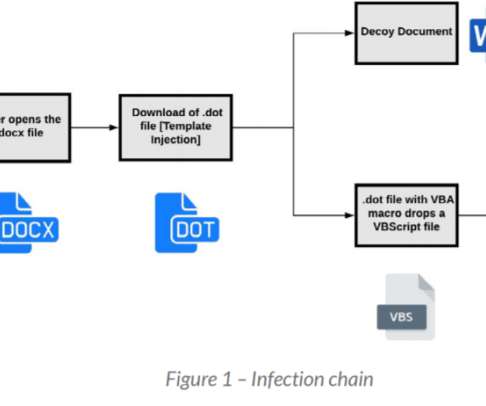
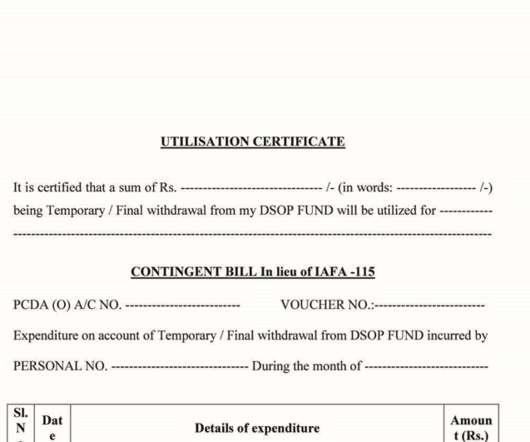
Ukraine’s CERT-UA revealed the national Delta military intelligence program has been targeted with a malware-based attack. The spear phishing messages were sent from a compromised e-mail address belonging to an employee of the Ministry of Defense, as well as messengers. ” states the Ukrainian military. .
















Let's personalize your content