Analyzing attacks conducted by North Korea-linked ARCHIPELAGO APT group
Security Affairs
APRIL 6, 2023
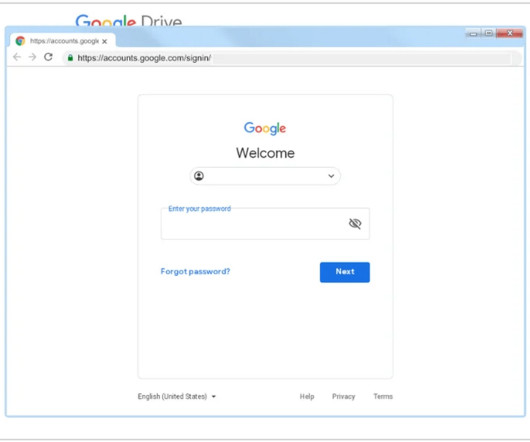
Google’s Threat Analysis Group (TAG) warns of a North Korea-linked cyberespionage group tracked as ARCHIPELAGO. TAG believes that the ARCHIPELAGO group is a subset of a threat actor tracked by Mandiant as APT43. ” reads the analysis published by Google TAG.












Let's personalize your content