From Cybercrime Saul Goodman to the Russian GRU
Krebs on Security
FEBRUARY 7, 2024
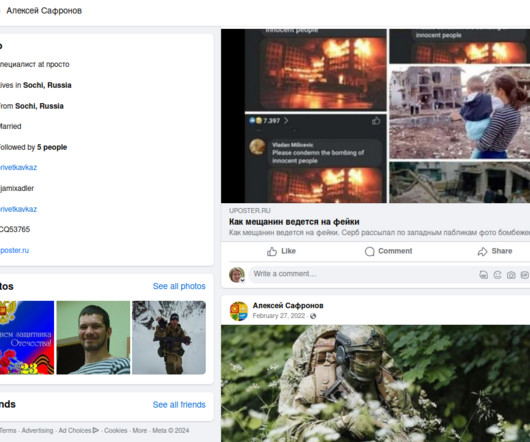
A review of this user’s hacker identities shows that during his time on the forums he served as an officer in the special forces of the GRU , the foreign military intelligence agency of the Russian Federation. “Remotely (in the form of constant support and consultations), or in person – this is discussed separately.

















Let's personalize your content