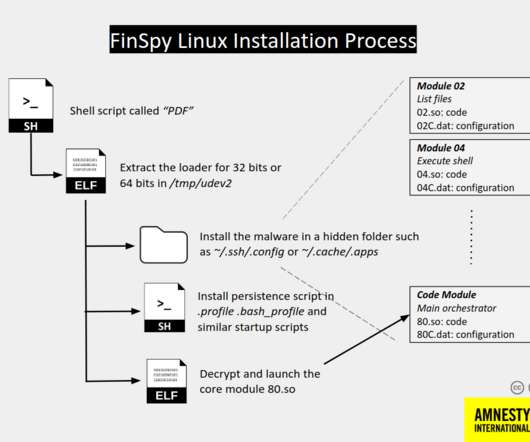
Unknown FinSpy Mac and Linux versions found in Egypt
Security Affairs
SEPTEMBER 27, 2020
Finisher, aka FinFisher, is a multiplatform surveillance software used by government and law enforcement agencies for their investigations, but unfortunately, it made the headlines because it was also used by oppressive regimes to spy on dissidents, activists, and Journalists. ” continues the analysis.


















Let's personalize your content