Anatomy of a Quantum Attack
Thales Cloud Protection & Licensing
APRIL 27, 2022
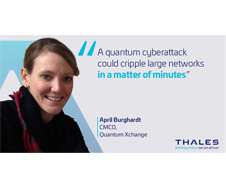
Each present a unique set of challenges and require equally powerful next-generation cyber security. A conventional computer would need 300 trillion years to break RSA encryption – considered the gold standard for Public Key Encryption (PKE). But another, far more damaging, attack vector is looming – quantum attack.













Let's personalize your content