Nodersok malware delivery campaign relies on advanced techniques
Security Affairs
SEPTEMBER 28, 2019
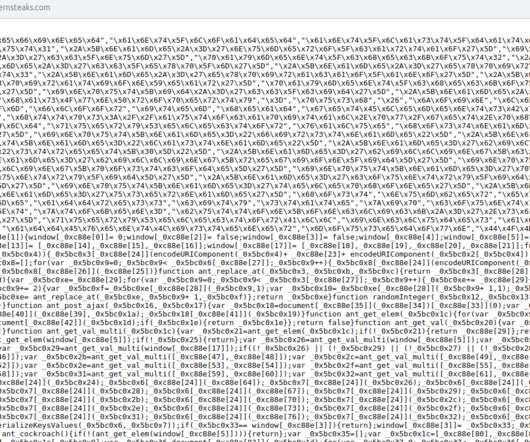
About 3% of the infected systems belong to organizations in different sectors, including education, professional services, healthcare, finance, and retail. One of the second-stage instances of PowerShell downloads the legitimate node.exe tool, while another drops WinDivert packet capture library components. ” Microsoft concludes.












Let's personalize your content