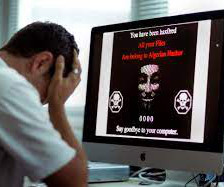
ToxicEye RAT exploits Telegram communications to steal data from victims
Security Affairs
APRIL 24, 2021
. “The bot is embedded into the ToxicEye RAT configuration file and compiled into an executable file (an example of a file name we found was ‘paypal checker by saint.exe’). ” Experts pointed out that the RAT can be also delivered by opening a malicious document (solution.doc) by pressing on “enable content.”.














Let's personalize your content