Breach Exposes Users of Microleaves Proxy Service
Krebs on Security
JULY 28, 2022
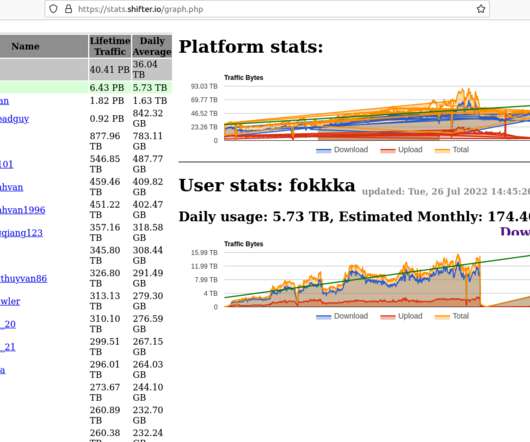
Microleaves , a ten-year-old proxy service that lets customers route their web traffic through millions of Microsoft Windows computers, recently fixed a vulnerability in their website that exposed their entire user database. June 22, 2022: Meet the Administrators of the RSOCKS Proxy Botnet. ” A teaser from Irish Tech News.














Let's personalize your content