We infiltrated an IRC botnet. Here’s what we found
Security Affairs
NOVEMBER 19, 2020
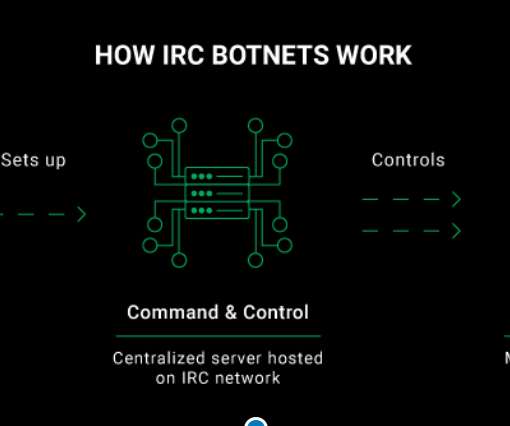
To conduct this investigation, a CyberNews researcher infiltrated an IRC botnet that we captured in one of our honeypots. That’s why our researchers use multiple cyberattack detection strategies and are always on the lookout for possible interception and infiltration opportunities. Our honeypot setup. Here’s how it all happened.













Let's personalize your content