Chinese Cyberespionage Group Expands Malware Arsenal
Data Breach Today
JULY 23, 2024
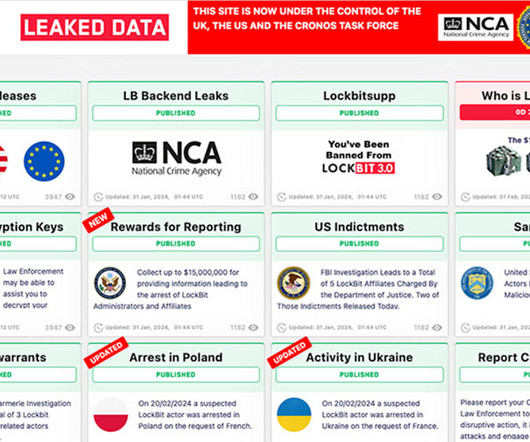
Symantec Traces 2021 Hong Kong Waterhole Attacks to Daggerfly Security researchers say they've traced a spate of backdoor attacks during 2021 against pro-democracy activists in Hong Kong to a Chinese cyberespionage group that's recently re-tooled its arsenal. The group is tracked by the Symantec Threat Hunter Team as Daggerfly.











































Let's personalize your content