Connecticut Tightens its Data Breach Notification Laws
Data Protection Report
OCTOBER 3, 2021
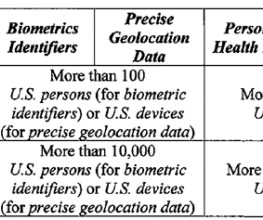
The amendment: Expands the definition of “personal information”; Shortens the notification deadline after discovery of a breach from 90 to 60 days; Removes the requirement to consult with law enforcement as part of a risk assessment; Deems compliant any person subject to and in compliance with HIPAA and HITECH; and.





















Let's personalize your content