TrickGate, a packer used by malware to evade detection since 2016
Security Affairs
JANUARY 31, 2023
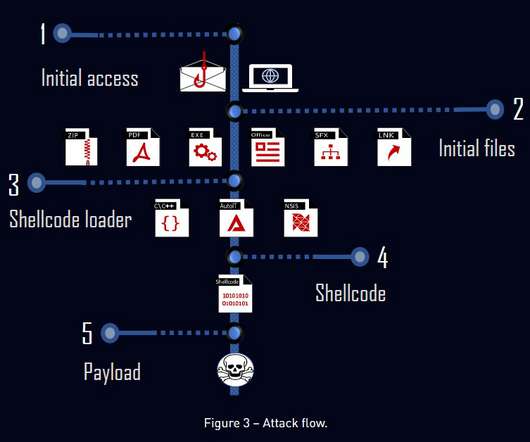
“The first stage mainly comes in the form of an archived executable, but we monitored many file types and delivery permutations that lead to the same shellcode.” The attack chain observed by the experts can vary significantly, but in most cases, threat actors used phishing messages with malicious attachments or malicious links.










Let's personalize your content