French Firms Rocked by Kasbah Hacker?
Krebs on Security
MARCH 2, 2020
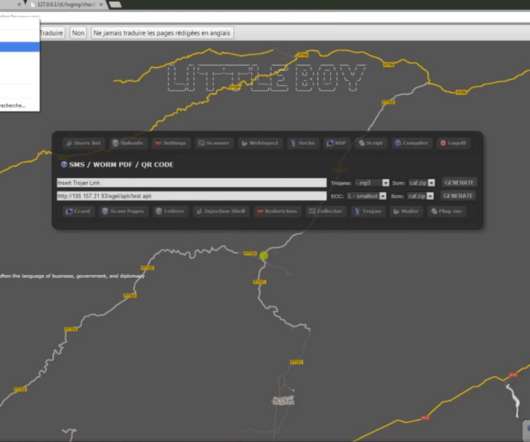
An individual thought to be involved has earned accolades from the likes of Apple , Dell , and Microsoft for helping to find and fix security vulnerabilities in their products. In 2018, security intelligence firm HYAS discovered a malware network communicating with systems inside of a French national power company.
















Let's personalize your content