New APT ChamelGang Targets energy and aviation companies in Russia
Security Affairs
OCTOBER 4, 2021
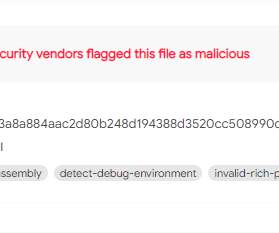
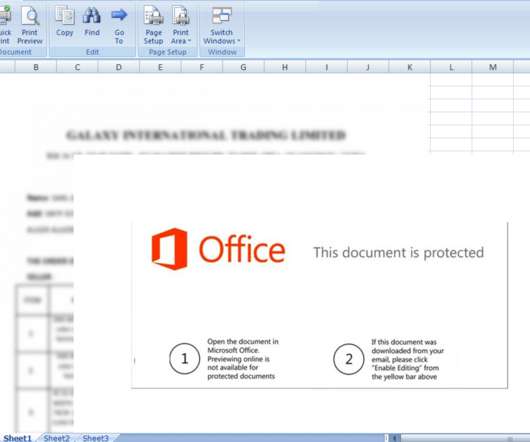
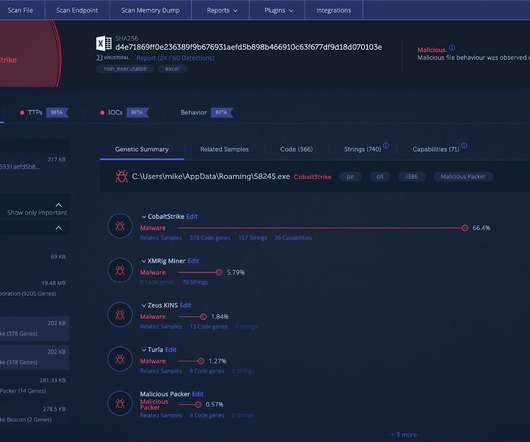
ChamelGang APT is a new cyberespionage group that focuses on fuel and energy organizations and aviation industry in Russia. ChamelGang is a new APT group that was first spotted in March by researchers at security firm Positive Technologies, it targets Russian companies in the energy and aviation industry. ” concludes the report.












Let's personalize your content