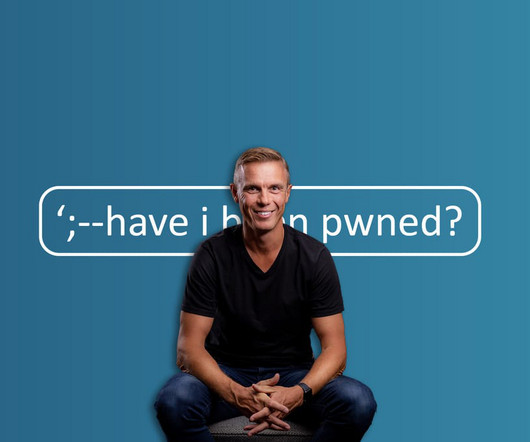
A Decade of Have I Been Pwned
Troy Hunt
DECEMBER 3, 2023
And that's precisely what this 185th blog post tagging HIBP is - the noteworthy things of the years past, including a few things I've never discussed publicly before. ” Anyone can type in an email address into the site to check if their personal data has been compromised in a security breach.










Let's personalize your content