Weakness at the Network Edge: Mandiant Examines 2022’s Zero-Day Exploits
eSecurity Planet
MARCH 27, 2023
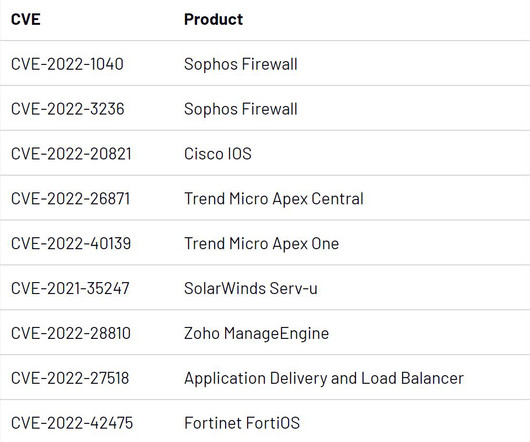
Enterprise IT, network and security product vulnerabilities were among those actively exploited in zero-day attacks last year, according to a recent Mandiant report. A quarter were financially motivated, and three of those were linked to ransomware operations. firewalls, IPS/IDS appliances, etc.),” the researchers wrote.











Let's personalize your content