PseudoManuscrypt, a mysterious massive cyber espionage campaign
Security Affairs
DECEMBER 16, 2021
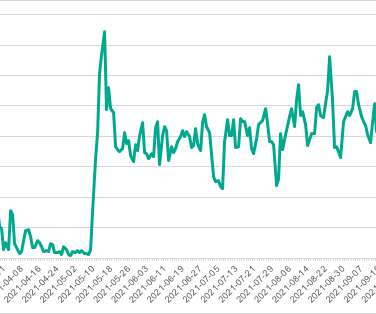
Kaspersky researchers reported that tens of thousands of devices belonging to industrial and government organizations worldwide have been hit by the PseudoManuscrypt spyware. Thus, we cannot say for certain whether the campaign is pursuing criminal mercenary goals or goals correlating with some governments’ interests.













Let's personalize your content