Meet Ika & Sal: The Bulletproof Hosting Duo from Hell
Krebs on Security
JANUARY 8, 2024
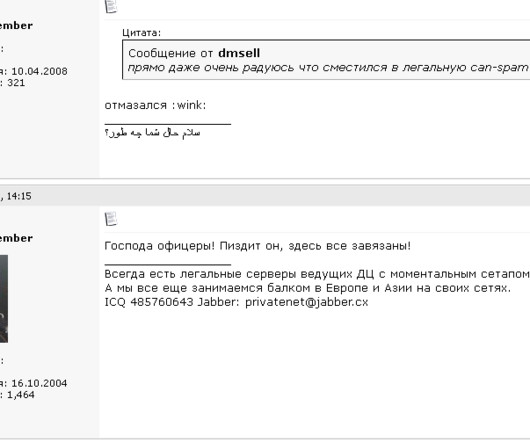
Spamit), an invite-only community for Russian-speaking people in the businesses of sending spam and building botnets of infected computers to relay said spam. Penchukov) — fled his mandatory military service orders and was arrested in Geneva, Switzerland. The Spamdot admins went by the nicknames Icamis (a.k.a. 9, 2024).












Let's personalize your content