Kali Linux Penetration Testing Tutorial: Step-By-Step Process
eSecurity Planet
APRIL 7, 2023
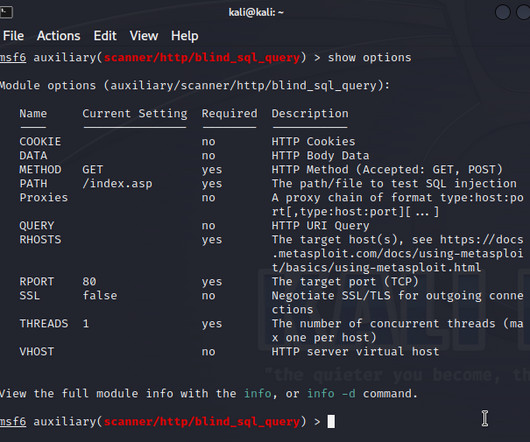
You may use a VPN or install utilities to capture and forward traffic to other subnets, or configure proxychains. Of course, you need an explicit consent, which is usually a legal agreement, to run a pentest, but you must also define the scope very precisely before the operation. Of course, some cases may require other tools.












Let's personalize your content