City of Dallas has set a budget of $8.5 million to mitigate the May Royal ransomware attack
Security Affairs
SEPTEMBER 23, 2023
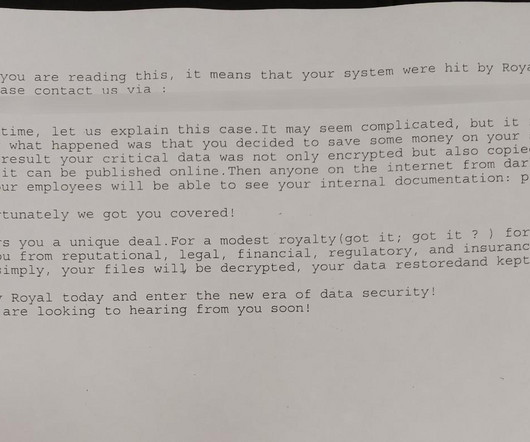
Once obtained access to the City’s network, the group performed reconnaissance and information-gathering activities using legitimate third-party remote management tools. The Royal group began reconnaissance activity in April 2023, and the analysis of system log data dates the beginning of the surveillance operations on April 7, 2023.










Let's personalize your content