InvisiMole group targets military sector and diplomatic missions in Eastern Europe
Security Affairs
JUNE 18, 2020
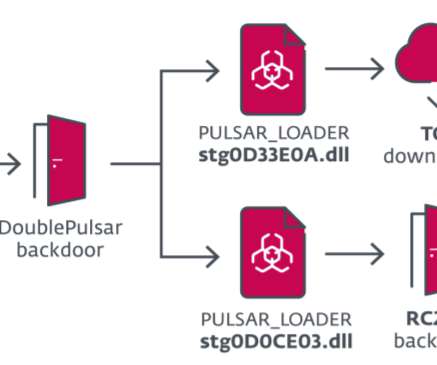
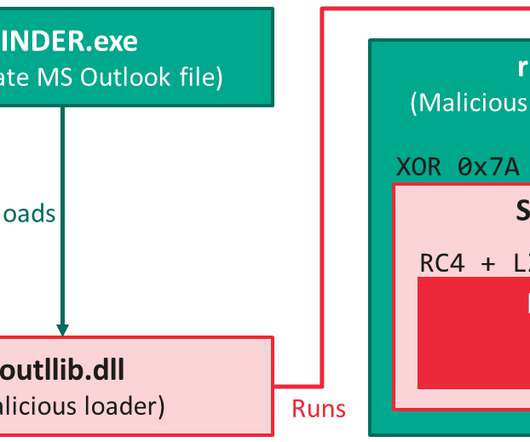
Security researchers at ESET recently uncovered a campaign carried out by the InvisiMole group that has been targeting a small number of high-profile organizations in the military sector and diplomatic missions in Eastern Europe. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Pierluigi Paganini.











Let's personalize your content