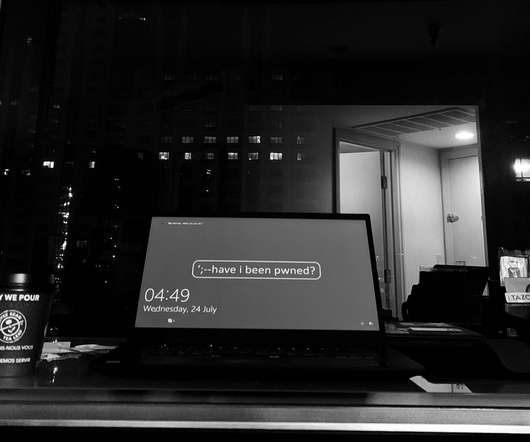
The Scammers’ Playbook: How Cybercriminals Get Ahold of Your Data
eSecurity Planet
SEPTEMBER 14, 2022
Often, a scammer will simply target the people in a company and fool them into giving up their personal details, account passwords, and other sensitive information and gain access that way. With all this in mind, let’s take a look at what a scammer does, who they target, and how to spot one trying to pick your metaphorical pockets.










Let's personalize your content