Iran-linked Mint Sandstorm APT targeted US critical infrastructure
Security Affairs
APRIL 19, 2023
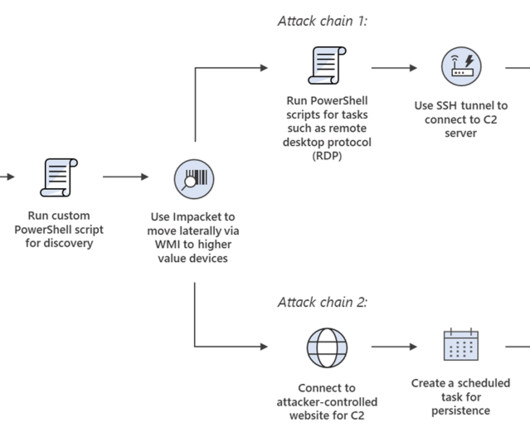
Mint Sandstorm also used custom tools in selected targets, notably organizations in the energy and transportation sectors. The group rapidly weaponized N-day vulnerabilities in popular enterprise applications by using publicly disclosed POCs.













Let's personalize your content