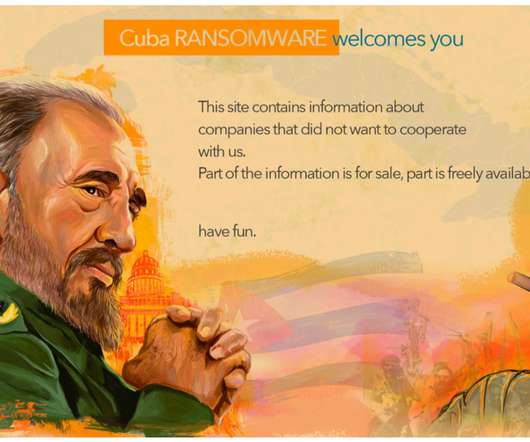
Connecting the Bots – Hancitor fuels Cuba Ransomware Operations
Security Affairs
MAY 7, 2021
As of April 28, the site mentioned nine companies primarily from aviation, financial, education and manufacturing industries. An example of spam email content Clicking the malicious link obviously leads to downloading a weaponized document. Usually, Hancitor is distributed via spam campaigns. Built-in tools were also abused.












Let's personalize your content