Crooks manipulate GitHub’s search results to distribute malware
Security Affairs
APRIL 13, 2024
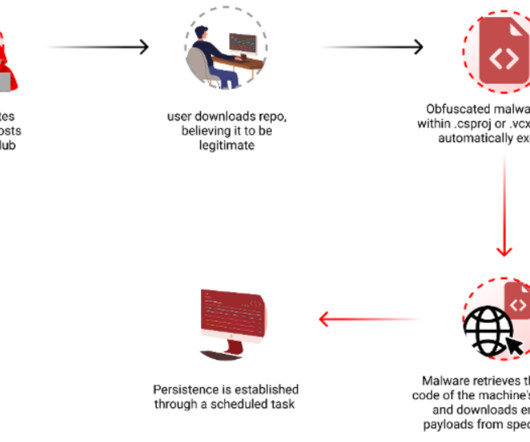
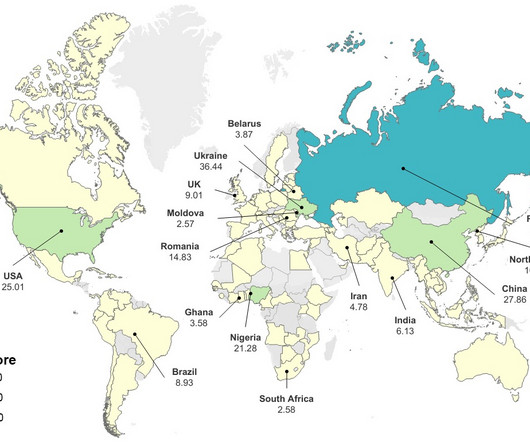
Researchers warn threat actors are manipulating GitHub search results to target developers with persistent malware. Checkmarx researchers reported that t hreat actors are manipulating GitHub search results to deliver persistent malware to developers systems. Attackers behind this campaign create malicious repositories with popular names and topics, they were observed using techniques like automated updates and fake stars to boost search rankings. “By leveraging GitHub Actions, the attacker














Let's personalize your content