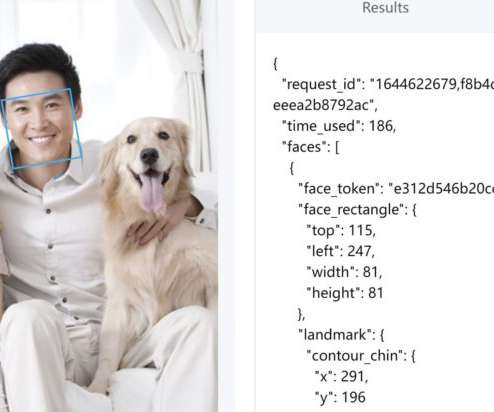
Best Facial Recognition Software for Enterprises In 2022
eSecurity Planet
FEBRUARY 11, 2022
Most essentially, facial recognition technology promises a solid amount of internal and external security advantages in the day-to-day activity of enterprises, making it a key technology for passwordless authentication. Also read: Passwordless Authentication 101. False Negatives, Deepfakes and Other Concerns.











Let's personalize your content