Microsoft warns of Dexphot miner, an interesting polymorphic threat
Security Affairs
NOVEMBER 26, 2019
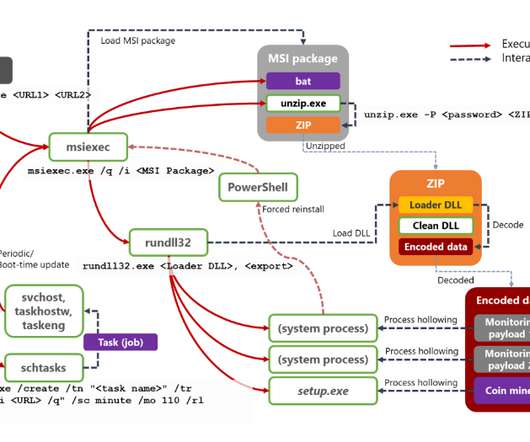
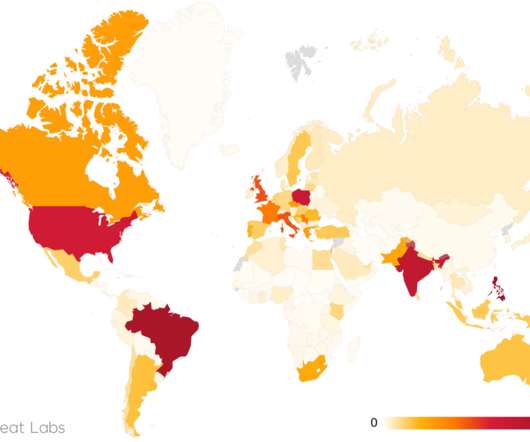
Security experts at Microsoft analyzed a new strain of cryptocurrency miner tracked as Dexphot that has been active since at least October 2018. The malicious code abuse of the resources of the infected machine to mine cryptocurrency , according to the experts it has already infected 80,000 computers worldwide.













Let's personalize your content