City of Dallas has set a budget of $8.5 million to mitigate the May Royal ransomware attack
Security Affairs
SEPTEMBER 23, 2023
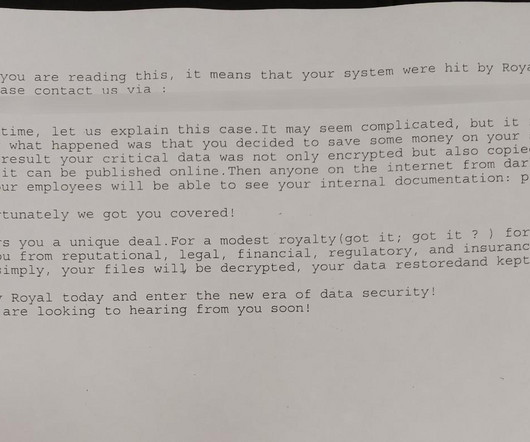
The City experts believe that the group specifically targeted a prioritized list of servers using legitimate Microsoft system administrative tools. million to mitigate the May Royal ransomware attack appeared first on Security Affairs.











Let's personalize your content