Why You Need to Tune EDR to Secure Your Environment
eSecurity Planet
APRIL 21, 2022
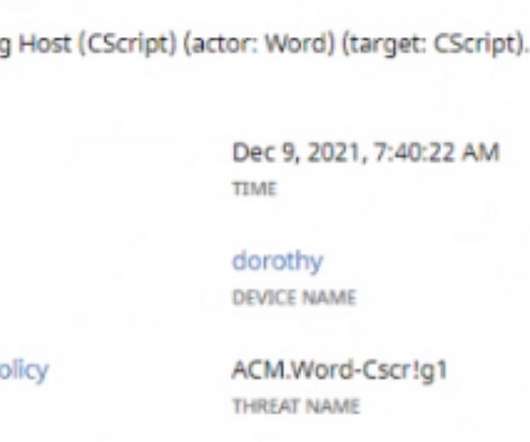
This allows EDR to deploy very quickly, but it also allows for a number of security vulnerabilities. Here we’ll discuss why EDR vendors choose these configurations, and how organizations can tune their EDR systems to fit their organization and improve security. Also read: 10 Top Active Directory Security Tools.










Let's personalize your content