RedEnergy Stealer-as-a-Ransomware employed in attacks in the wild
Security Affairs
JULY 5, 2023
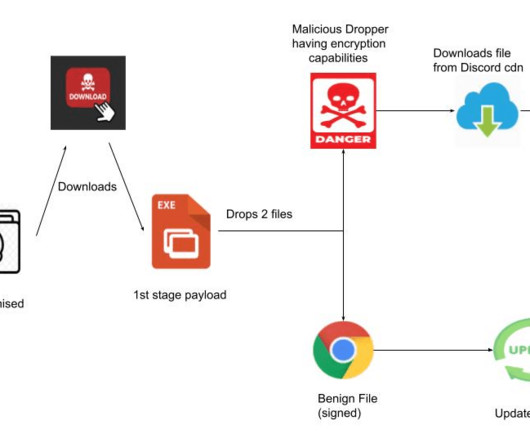
RedEnergy is a sophisticated stealer-as-a-ransomware that was employed in attacks targeting energy utilities, oil, gas, telecom, and machinery sectors. Zscaler ThreatLabz researchers discovered a new Stealer-as-a-Ransomware named RedEnergy used in attacks against energy utilities, oil, gas, telecom, and machinery sectors.










Let's personalize your content