Kali Linux Penetration Testing Tutorial: Step-By-Step Process
eSecurity Planet
APRIL 7, 2023
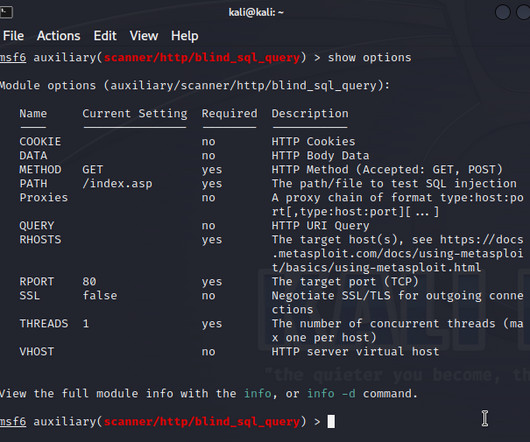
In this article, we’ll focus primarily on how to use this powerful OS to run a pentest and mistakes to avoid. You may use a VPN or install utilities to capture and forward traffic to other subnets, or configure proxychains. Of course, some cases may require other tools. If you don’t like manual setups (e.g.,













Let's personalize your content