Kali Linux Penetration Testing Tutorial: Step-By-Step Process
eSecurity Planet
APRIL 7, 2023
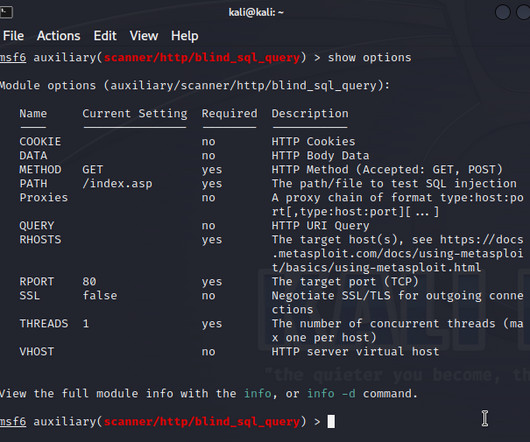
You may use a VPN or install utilities to capture and forward traffic to other subnets, or configure proxychains. phishing) Memory corruptions Wi-Fi attacks Kali is a wonderful toolbox, because it has tools for a wide range of pentests. Besides, attacking tools can send multiple probes or headers along with their requests (e.g.,








Let's personalize your content