Russia-linked APT28 compromised Ubiquiti EdgeRouters to facilitate cyber operations
Security Affairs
FEBRUARY 28, 2024
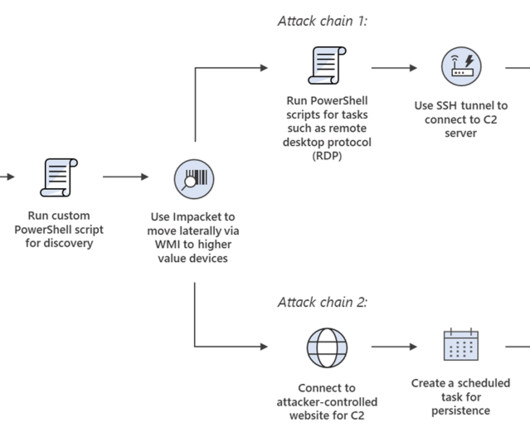
. “As early as 2022, APT28 actors had utilized compromised EdgeRouters to facilitate covert cyber operations against governments, militaries, and organizations around the world.” and foreign governments and military, security, and corporate organizations. ” reads the joint report.














Let's personalize your content