Hackers Are Now Exploiting Windows Event Logs
eSecurity Planet
MAY 10, 2022
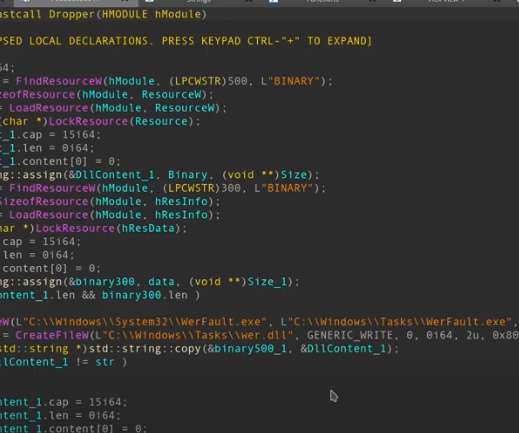
The system uses DLL (Dynamic Link Library) files to store some resources the application needs and will load automatically. If it does not find one, the encrypted shell code is written in 8KB chunks in the event logs. The attackers used two types of Trojans: HTTP-based Trojan with C2 (command and control) Named-pipe based Trojan.









Let's personalize your content