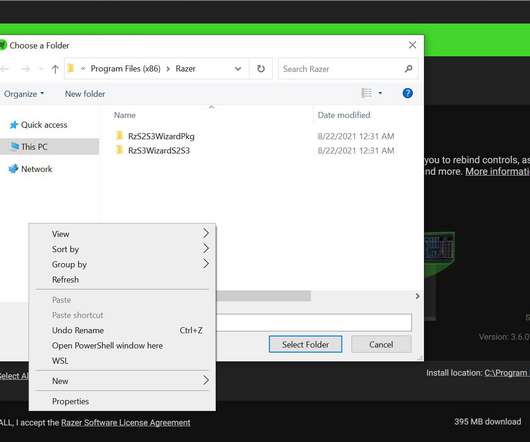
LPE zero-day flaw in Razer Synapse allows attackers to take over Windows PCs
Security Affairs
AUGUST 23, 2021
Razer is a popular manufacturer of computer accessories, including gaming mouses and keyboards. Razer is a very popular computer peripherals manufacturer that designs, develops, and sells consumer electronics, financial services, and gaming hardware, including gaming mouses and keyboards.















Let's personalize your content