Kali Linux Penetration Testing Tutorial: Step-By-Step Process
eSecurity Planet
APRIL 7, 2023
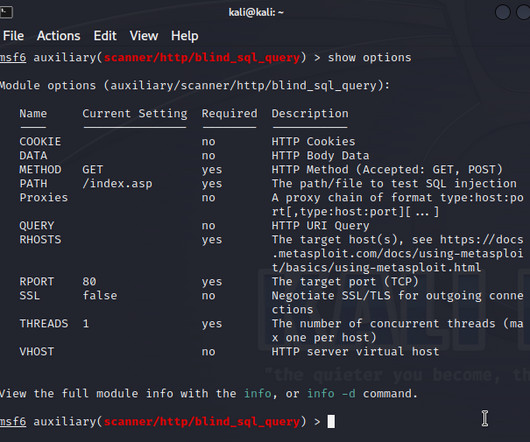
You may use a VPN or install utilities to capture and forward traffic to other subnets, or configure proxychains. The category usually matches the typical phases of a pentest, like “information gathering” or “post-exploitation,” but also recurrent tasks, such as “password attacks.” You’ll need the “security” edition.








Let's personalize your content