Cyber-Criminal espionage Operation insists on Italian Manufacturing
Security Affairs
MAY 22, 2020
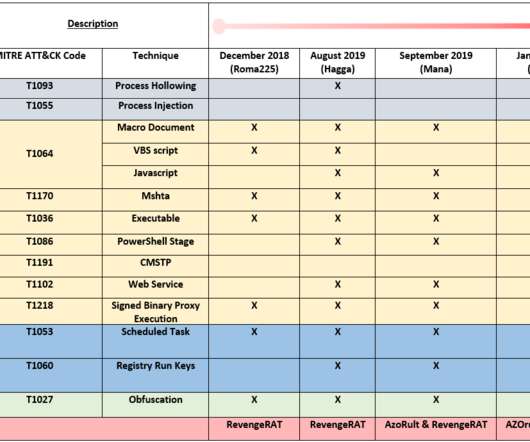
The group behind this activity is the same we identified in the past malicious operations described in Roma225 (12/2018), Hagga (08/2019), Mana (09/2019), YAKKA (01/2020). All threats use at least one obfuscation method to make the analysis harder. Technical Analysis. Load($_PMP);$_1.EntryPoint.invoke($S,$X)”,









Let's personalize your content