Russia-linked APT28 used post-compromise tool GooseEgg to exploit CVE-2022-38028 Windows flaw
Security Affairs
APRIL 22, 2024
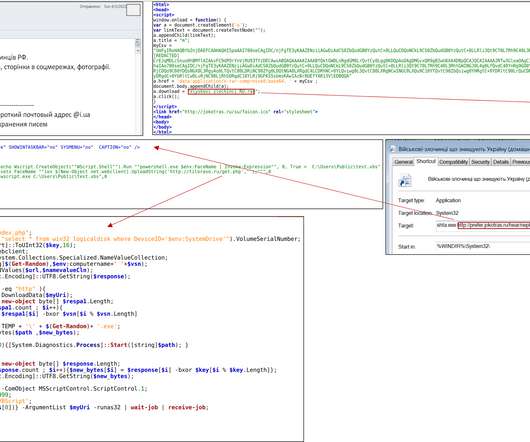
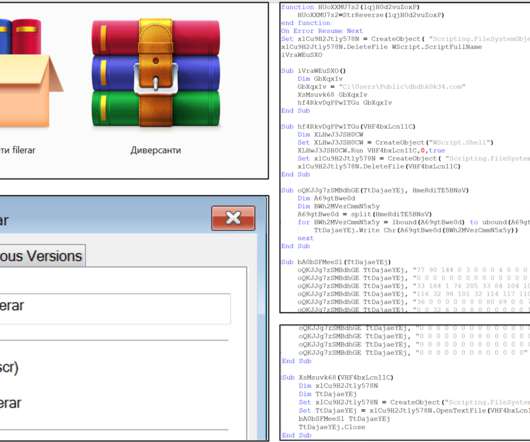
This tool modifies a JavaScript constraints file and executes it with SYSTEM-level permissions. GooseEgg is usually deployed with a batch script, commonly named execute.bat or doit.bat. This script creates a file named servtask.bat, which includes commands for saving or compressing registry hives.










Let's personalize your content