Who and What is Behind the Malware Proxy Service SocksEscort?
Krebs on Security
JULY 25, 2023
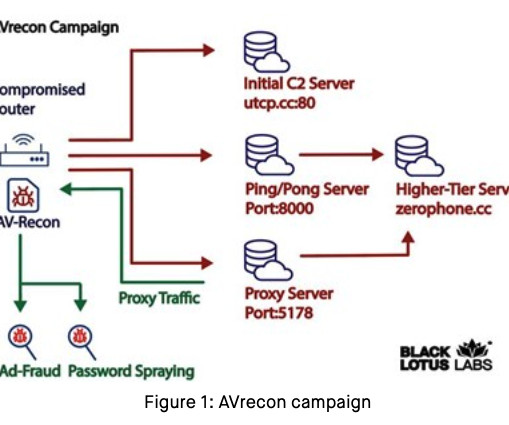
Danny Adamitis , principal information security researcher at Lumen and co-author of the report on AVrecon, confirmed Kilmer’s findings, saying the C2 data matched up with what Spur was seeing for SocksEscort dating back to September 2022. SocksEscort began in 2009 as “ super-socks[.]com












Let's personalize your content