The Intelligent Information Management Starting Line – 3 Tasks to Target Now by AIIM
IG Guru
MAY 28, 2019
The post The Intelligent Information Management Starting Line – 3 Tasks to Target Now by AIIM appeared first on IG GURU. Download the PDF.

 the-intelligent-information-management-starting-line-3-tasks-to-target-now
the-intelligent-information-management-starting-line-3-tasks-to-target-now 
IG Guru
MAY 28, 2019
The post The Intelligent Information Management Starting Line – 3 Tasks to Target Now by AIIM appeared first on IG GURU. Download the PDF.

AIIM
JUNE 25, 2019
Organizations around the world invest a great deal of time and money to manage information. So, if you have a $50 million company you can anticipate that you’ll spend around $3 million or so to manage your information every year. Evaluating your current information stores and processes.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

IBM Big Data Hub
FEBRUARY 13, 2024
Generative AI ( artificial intelligence ) promises a similar leap in productivity and the emergence of new modes of working and creating. They are now capable of natural language processing ( NLP ), grasping context and exhibiting elements of creativity. Automate tedious, repetitive tasks.
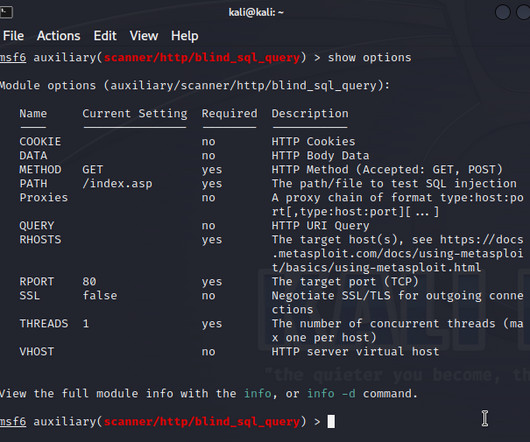
eSecurity Planet
APRIL 7, 2023
For now, Kali is primarily known for its roughly 600 open source pentesting tools, allowing pentesters to easily install a full range of offensive security tools. Pentesting basics A penetration test aims to emulate a real attack on a targeted system. Also read: 24 Top Open Source Penetration Testing Tools What Is Penetration Testing?

Advertisement
Many application teams leave embedded analytics to languish until something—an unhappy customer, plummeting revenue, a spike in customer churn—demands change. But by then, it may be too late. In this White Paper, Logi Analytics has identified 5 tell-tale signs your project is moving from “nice to have” to “needed yesterday.".

eSecurity Planet
AUGUST 10, 2023
Threat intelligence feeds are continually updated streams of data that inform users of different cybersecurity threats, their sources, and any infrastructure impacted or at risk of being impacted by those threats. To get a better idea of what each top threat intelligence feed solution offers, take a look at our comparison table below.

KnowBe4
JUNE 13, 2023
CyberheistNews Vol 13 #24 | June 13th, 2023 [The Mind's Bias] Pretexting Now Tops Phishing in Social Engineering Attacks The New Verizon DBIR is a treasure trove of data. They explained: "Now, who has received an email or a direct message on social media from a friend or family member who desperately needs money? Probably fewer of you.
Let's personalize your content