How Data Changes the Cyber-Insurance Market Outlook
Dark Reading
OCTOBER 16, 2023
By using data to drive policy underwriting, cyber-insurance companies can offer coverage without a price tag that drives customers away.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 tag
tag  Marketing Related Topics
Marketing Related Topics 
Dark Reading
OCTOBER 16, 2023
By using data to drive policy underwriting, cyber-insurance companies can offer coverage without a price tag that drives customers away.

Dark Reading
MARCH 29, 2023
Google TAG researchers reveal two campaigns against iOS, Android, and Chrome users that demonstrate how the commercial surveillance market is thriving despite government-imposed limits.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Krebs on Security
APRIL 15, 2024
Image: Camdenliving.com Also, the fobs pass the credentials to his front door over the air in plain text, meaning someone could clone the fob just by bumping against him with a smartphone app made to read and write NFC tags. Neither August nor Chirp Systems responded to requests for comment. It’s either agree to use the app or move.”

RFID Global Solution, Inc.
JULY 15, 2017
Driven by lower prices of radio-frequency identification (RFID) tags, and increasing penetration of RFID technology in various industries, the RFID market is likely to witness high growth in coming years. The RFID market was valued at USD 16.95 The report also provides a detailed overview of the value chain of the RFID market.

Advertisement
Just by embedding analytics, application owners can charge 24% more for their product. How much value could you add? This framework explains how application enhancements can extend your product offerings. Brought to you by Logi Analytics.

RFID Global Solution, Inc.
JULY 15, 2017
MarketsandMarkets June 2017 Driven by lower prices of radio-frequency identification (RFID) tags, and increasing penetration of RFID technology in various industries, the RFID market is likely to witness high growth in coming years. The RFID market was valued at USD 16.95 Billion in 2016 and is expected to grow at a CAGR of 7.7%

eSecurity Planet
JUNE 1, 2023
To avoid issues, we need to understand the DMARC record tags in detail. DMARC Record Tags in Detail To understand the DMARC record, we start with an example record and then explore the detailed options for each tag. Tags are separated by semicolons ( ; ) with no extra spaces.

DLA Piper Privacy Matters
AUGUST 1, 2019
While the previous version made it clear that advertising displayed online “ to the general public ” was excluded from the scope of these rules (suggesting targeted advertising was covered), new changes suggest that even targeted advertising might not constitute direct marketing communications under the Proposal (e.g.

OpenText Information Management
FEBRUARY 8, 2024
The goal is to create an inclusive experience where all PDFs and documents are crafted with accessibility in mind or appropriate tags are added for those who require such features. Accessible PDFs are easy to use – enabling most people to view, read or interact with them.

Collibra
NOVEMBER 16, 2021
Object tagging and ML-powered automation tagging . Another Snowflake governance feature is object tagging. Object Tagging makes it easier to know and control your data by applying business context, such as tags that identify data objects as sensitive, PII or belonging to a cost center. But we also see the gaps.

The Last Watchdog
NOVEMBER 19, 2018
Assuming privacy concerns get addressed, much wider consumer uses are envisioned in areas such as marketing, retailing and health services. According to Allied Market Research, the facial recognition systems market is in the midst of rising at a compounded annual growth rate of 21% between 2016 to 2022. billion by 2022.

DLA Piper Privacy Matters
JANUARY 19, 2022
The new “Administrative Regulations on Algorithm Recommendation of Internet Business Services” comes into force on 1 March 2022, and will introduce important rules on the use of algorithms when operating digital platforms/websites/apps – including targeted marketing – in China.

Info Source
JULY 12, 2018
For photographs, we analyze and tag the content. I know both ends of the market, having worked with an enterprise product in Documentum and run a small business myself.”. We will always release new features in tiers taking into account feedback we receive from the market.

Synergis Software
OCTOBER 25, 2021
He has been instrumental in the implementation of all our enterprise solutions, including our CRM, marketing automation solutions, ERP, and a Professional Services Administration tool, to name a few. Eric also oversees our internal helpdesk team and often tags in to support the organization when he’s not involved in larger projects.

IBM Big Data Hub
AUGUST 28, 2023
With nearly 5 billion users worldwide—more than 60% of the global population —social media platforms have become a vast source of data that businesses can leverage for improved customer satisfaction, better marketing strategies and faster overall business growth. noun, verb, adjective, etc.),
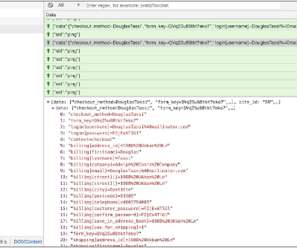
Security Affairs
NOVEMBER 15, 2020
Once executed, a malicious JavaScript file is requested from the a C2 server (at https[:]//tags-manager[.]com/gtags/script2 The distinctive aspect of this attack is the use of WebSockets, instead of HTML tags or XHR requests, to extract the information from the compromised site that makes this technique more stealth.

Security Affairs
FEBRUARY 12, 2024
Whether it’s for gathering market intelligence, ensuring your privacy, or bypassing geographical restrictions, proxies have become the unsung heroes for individuals and enterprises alike. Imagine you’re doing market research and you need access to local pricing across different regions.
Security Affairs
JANUARY 21, 2024
CISA warns of actively exploited Ivanti EPMM flaw CVE-2023-35082 The Quantum Computing Cryptopocalypse – I’ll Know It When I See It Kansas State University suffered a serious cybersecurity incident CISA adds Chrome and Citrix NetScaler to its Known Exploited Vulnerabilities catalog Google TAG warns that Russian COLDRIVER APT is using a custom backdoor (..)

John Battelle's Searchblog
MAY 10, 2010
We're used to buzz around Apple, and in particular, we're quite used to buzz about how Apple goes to market. CEO Steve Jobs is widely considered the greatest marketer alive, and nearly every marketer I've worked with has expressed sincere admiration for the magic the man is capable of weaving. Classic Jobs). Think I’m kidding?

Interactive Information Management
DECEMBER 6, 2013
At KME (a DC SEO Company and Digital Technology Agency ), we cover a lot of ground among client types, industry segments and technology services, with a heavy emphasis on area DC SEO business requirements for online, interactive marketing and advertising.
Security Affairs
AUGUST 6, 2023
Reptile Rootkit employed in attacks against Linux systems in South Korea New PaperCut flaw in print management software exposes servers to RCE attacks A cyberattack impacted operations of multiple hospitals in several US states Married couple pleaded guilty to laundering billions in cryptocurrency stolen from Bitfinex in 2016 Malicious packages in (..)

Security Affairs
DECEMBER 10, 2021
“After analysis and confirmation by the White Hat Security Research Institute, there are currently many popular systems on the market that are affected. Query our API for "tags=CVE-2021-44228" for source IP addresses and other IOCs. .” reads the post published by the Alibaba Coud security team.

IBM Big Data Hub
OCTOBER 16, 2023
Machine learning in marketing and sales According to Forbes , marketing and sales teams prioritize AI and ML more than any other enterprise department. Marketers use ML for lead generation, data analytics, online searches and search engine optimization (SEO). Then, it can tailor marketing materials to match those interests.
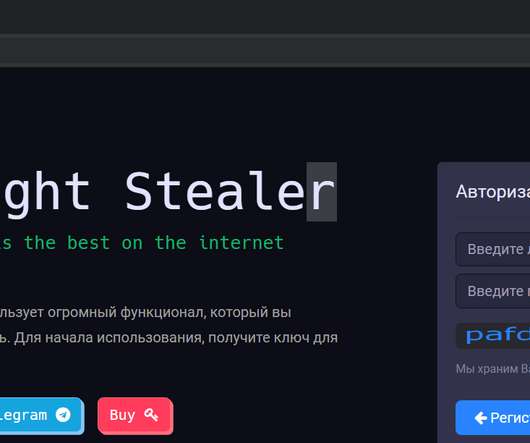
Security Affairs
MAY 7, 2020
Infostealer market is one of the most remunerative for cyber criminals, information gathered from infected systems could be resold in the cybercrime underground or used for credential stuffing attacks. The first information tag “ prog.params ” is immediately retrieved in the instruction “ HandlerParams.Start() ” seen in Figure 4.

eSecurity Planet
MARCH 21, 2022
” As XDR and SASE are largely separate markets, focusing on them separately will “accelerate those roadmaps and their value to customers,” Rittenhouse said. Bringing the technology to the market quickly is the primary purpose of this.” Employees can also tag data as sensitive.

Security Affairs
MARCH 27, 2024
DDR would, in effect, “tag” data so that a GPS-type homing beacon would keep a gapless record of where it went, who accessed it, what they did with it, and (with the help of some cyber sleuthing) perhaps why. The second benefit is what we’ll be focusing on today. DDR Knows What Your Data Did Last Summer Then, along came a revolutionary idea.

eSecurity Planet
SEPTEMBER 7, 2023
This has also been evident in declining venture capital funding for startups and the slumping IPO market too. As for the price tag on the deal, it’s estimated at $200 to $250 million. Those investors took a big haircut on the deal, but those kinds of discounts are what will get the M&A market going again. Consulting.

IBM Big Data Hub
APRIL 18, 2024
While cost wasn’t the primary driver, it reflects a growing belief that the value generated by gen AI outweighs the price tag. Here are some areas where organizations are seeing a ROI: Text (83%) : Gen AI assists with automating tasks like report writing, document summarization and marketing copy generation.

The Last Watchdog
JUNE 30, 2021
Today’s websites integrate dozens of third-party service providers, from user analytics to marketing tags, CDNs , ads, media and these third-party services load their code and content into the browser directly. Supply chain attack tactics. Attackers have been using various techniques to exfiltrate sensitive data from websites.

Threatpost
SEPTEMBER 4, 2019
million price tag for a zero-click 0-day in Android. Exploit broker Zerodium has implemented a $2.5

John Battelle's Searchblog
JANUARY 19, 2023
Anything tagged as “ the talk of Davos ” is destined for a ritual media takedown, after all. I’m not sure that’s a huge, investable market, but it’s a leading indicator. ChatGPT, with the right guardrails, could probably do the same job – and for nearly no cost.

ForAllSecure
DECEMBER 6, 2022
Detailed documentation about API issues can be viewed in the application, where each issue is tagged, cross-referenced with the latest specs, sorted by the path it was found in, and assigned a severity score for easy remediation. This lets development teams avoid bottlenecks in the DLC and bring software to market faster.

Collibra
DECEMBER 1, 2020
For example, if you don’t have an approved taxonomy of what data exists in the business, then you can’t adequately tag data as it flows into your lake. Imagine the following scenario: Your company is launching a new product and wants to create a marketing campaign tailored to consumers who are most likely to purchase this new product.

Collibra
JANUARY 23, 2023
” At the same time, the federal government recognizes that “…… the technology market supporting enterprise-wide data categorization is still maturing ……” and sets out to play a long game. Reflected in the federal zero-trust strategy is the calling out of agencies’ data categorization directly fueling this maturity characteristic.
Krebs on Security
NOVEMBER 28, 2022
Pushwoosh admitted the LinkedIn profiles were fake, but said they were created by a marketing firm to drum up business for the company — not misrepresent its location. Pushwoosh employees posing at a company laser tag event. . “Pushwoosh never mentioned it was Russian-based in eight annual filings in the U.S.

Security Affairs
SEPTEMBER 4, 2019
We've also increased WhatsApp & iMessage (0-click) but reduced the payout for iOS (1-click) in accordance with market trends: [link] pic.twitter.com/XqpmAKmmKF — Zerodium (@Zerodium) September 3, 2019. For the first time, we will be paying more for Android than iOS. million, while an exploit chain for iOS only $2 million.

Security Affairs
OCTOBER 13, 2020
If you take a look at the global market for IoT, you can easily spot the trend. The market surpassed $100 billion in revenue, and it’s revenue for the 2025 projections tell us that it will hit $1.5 IoT market exploded because IoT devices offer more convenience, are easy to use, and bring true value. Irregular Updates.

John Battelle's Searchblog
JANUARY 6, 2018
digital marketing. digital marketing agency. digital marketing blog. marketing agency. marketing blog. digital marketing. digital marketing agency. digital marketing blog. marketing agency. marketing blog. Tags: advertising. advertising agency. alistair croll. architecture.

Everteam
MAY 6, 2019
For better visibility and proper decision making, everteam.iNSight allows you to search your data and retrieve media assets which will be found easily through metadata tags. If we take Marketers for example, through everteam.iNSight, they will no longer have to spend their time filtering and organizing data. Job Scheduler.

Everteam
MAY 22, 2019
For better visibility and proper decision making, everteam.iNSight allows you to search your data and retrieve media assets which will be found easily through metadata tags. If we take Marketers for example, through everteam.iNSight, they will no longer have to spend their time filtering and organizing data. Configurator. ? Security.

erwin
JANUARY 7, 2021
As a result, look for more automated compliance solutions to hit the market. AI-powered data governance will ensure data environments always stay up to date and controlled, enabling compliance and tagging of sensitive data. AI will drive automation to ensure an organization’s framework is always accurate and up to date.

OneHub
SEPTEMBER 14, 2020
For example, the marketing team will need to upload content to support the sales team, while the accounting team can use the CRM to ensure customers pay their invoices on time. A good chat tool will make it easy to tag someone in a conversation, too, so they can be notified when they’re outside the app.

IBM Big Data Hub
APRIL 24, 2024
The price tag can add up quickly. Example A marketing firm always conducts a PIA before every new market research project. Malicious hackers PII is a major target for cybercriminals, who can use it to commit identity theft, steal money, or sell it on the black market.
Krebs on Security
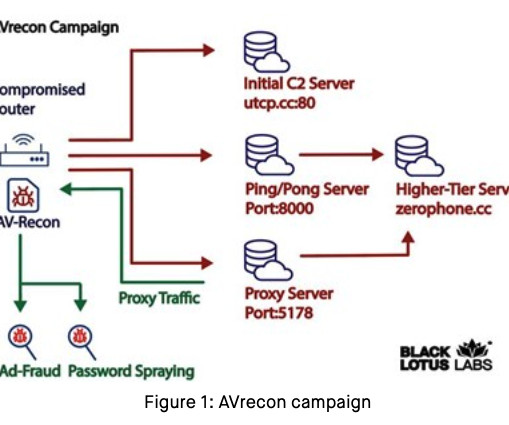
JULY 25, 2023
And a great many of these “proxy” networks are marketed primarily to cybercriminals seeking to anonymize their traffic by routing it through an infected PC, router or mobile device. SocksEscort[.]com com , is what’s known as a “SOCKS Proxy” service.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content