From Cybercrime Saul Goodman to the Russian GRU
Krebs on Security
FEBRUARY 7, 2024
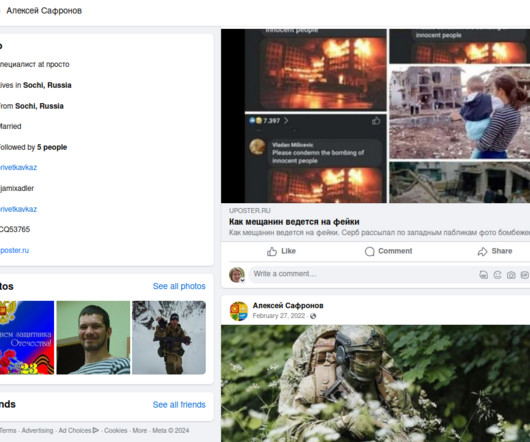
In 2021, the exclusive Russian cybercrime forum Mazafaka was hacked. The leaked user database shows one of the forum’s founders was an attorney who advised Russia’s top hackers on the legal risks of their work, and what to do if they got caught. A review of this user’s hacker identities shows that during his time on the forums he served as an officer in the special forces of the GRU , the foreign military intelligence agency of the Russian Federation.


































Let's personalize your content